Säkerhetsbrist i Google H1
H1 är Googles säkerhetschip som återfinnes i Chromebooks. Andra smeknamn för Google H1 är Cr50 eller G Chip.
Säkerhetsbristen som återfinnes i H1 har och göra med ECDSA signaturgenerering och gör att enbart 64 bitar istället för 256 bitar entropi används för den privata nyckeln. Enligt Google gör detta att det är möjligt för en angripare att återskapa den privata nyckeln:
We confirmed that the incorrect generation of the secret value allows it to be recovered, which in turn allows the the underlying ECC private key to be obtained
Denna ECDSA-nyckel används för U2F-inloggning mot webbplatser som erbjuder multifaktorautentisering. Detta innebär således att:
- Firmware måste uppdateras i H1-chippet. Detta görs automatiskt från och med ChromeOS 75 som släpptes 26:de Juni 2019
- Samtliga nycklar måste bytas ut mot de sajter där U2F används för multifaktorautentisering (MFA)
- Observera att detta enbart gäller om du använt Chromebookens strömknapp för inloggning samt MFA
Du kan även skriva in chrome://system i webbläsaren på din Chromebook och sedan titta efter cr50_version och RW-raden. Version 0.3.15 och senare innehåller ej denna sårbarhet.
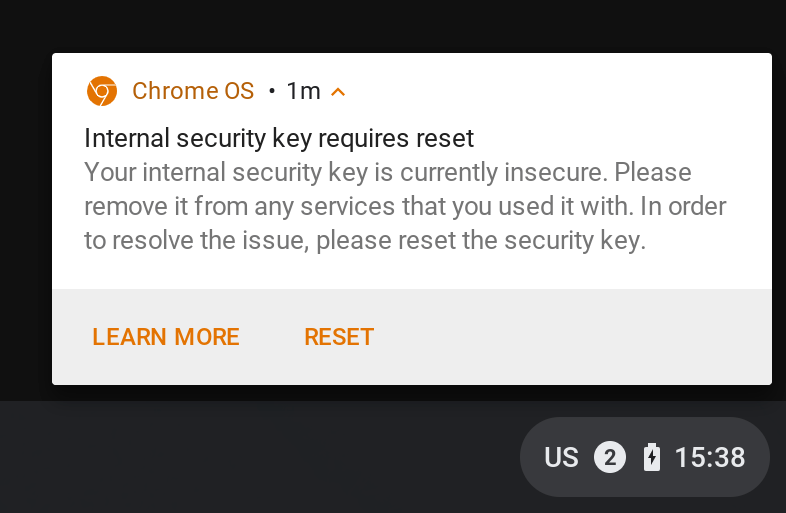
Följande meddelande ”Internal security key requires reset” visas för användare som är drabbade av denna säkerhetsbrist:

Detta är så klart en pinsam miss av Google och något som bör fångas upp av tester. Men att denna typ av sårbarheter ökar är något som jag tror vi kommer att få se mer av, det var exempelvis inte länge sedan som Feitian Security Key hade en sårbarhet (på bild till höger).
Bild på chip av Harrison Broadbent på Unsplash
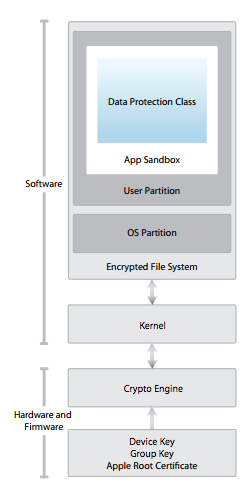
 Microsoft meddelade för ett tag sedan att man avser att stärka krypteringen i Windows under perioden 2012-2013 och nedan kan du se några av förbättringarna som håller på att införas.
Microsoft meddelade för ett tag sedan att man avser att stärka krypteringen i Windows under perioden 2012-2013 och nedan kan du se några av förbättringarna som håller på att införas.